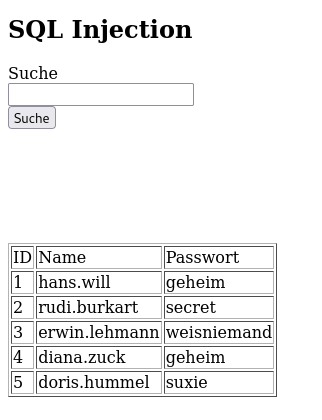
SQL Injection
Vorüberlegung
Verhaltensweise einer SQL Abfrage
- Normale Abfrage
- MariaDB [sql_injections]> select * from users where username = 'rudi.burkart';
+------+--------------+----------+ | id | username | password | +------+--------------+----------+ | 2 | rudi.burkart | secret | +------+--------------+----------+ 1 row in set (0.000 sec)
- Oder Verknüpfung
- MariaDB [sql_injections]> select * from users where username = 'rudi.burkart' or username = 'hans.will';
+------+--------------+----------+ | id | username | password | +------+--------------+----------+ | 2 | rudi.burkart | secret | | 1 | hans.will | geheim | +------+--------------+----------+ 2 rows in set (0.000 sec)
PHP Code
Unsicher
$search = $_POST['search'];
$sql = "SELECT * FROM users WHERE username='$search'";
$result = mysqli_query($link, $sql);
Sicher
$search = mysqli_real_escape_string($link, $_POST['search']); $sql = "SELECT * FROM users WHERE username='$search'"; $result = mysqli_query($link, $sql);